API Security
Security for application programming interfaces (APIs) is the process of reducing attacks on APIs. As they serve as the foundation for the backend of both mobile and online applications. Therefore, it is essential to safeguard the private information that people and organisations transfer.
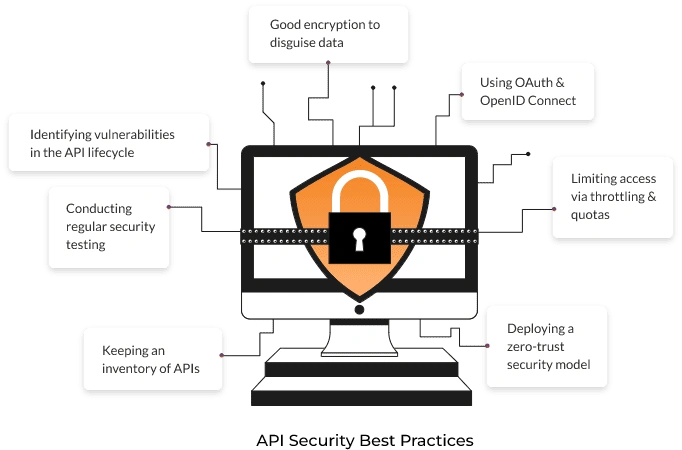
API security testing involves checking the endpoints of the API for security and dependability. This ensures that an application programme interface (API) complies with an organisation’s best practices.
API security testing checks off fundamental security criteria, such as those of user access, encryption, and authentication. The goal of API scanning is to provide inputs that would cause an API to exhibit errors and illogical behaviour, basically imitating the behaviours and attack methods of would-be hackers.

Got Questions Related to API Security Testing?
Contact Us NowWhat is API?
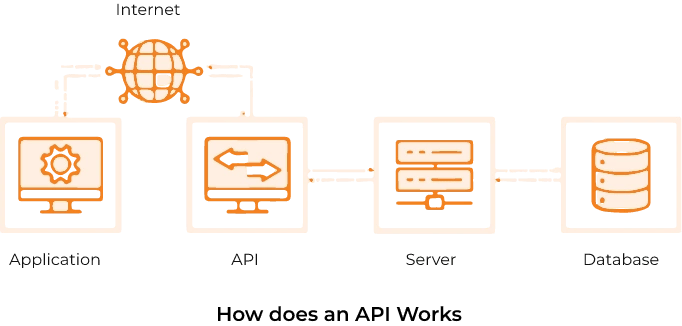
An API or Application Programme Interface, is a technique that permits communication between two software systems.
For instance, not all of the names of the streets, towns, cities, restaurants, movie theatres, and other landmarks are stored in your phone’s Google Maps programme. Instead, it establishes a connection to another Google server-based application that holds all of that data. An API is used to enable this connection.
API security has become more crucial, especially with the growth of IoT. Between users, APIs, and the programmes and systems they use, sensitive and important data is transmitted. An otherwise safe computer or network can be easily breached by hackers using an unsecured API. Man-in-the-middle (MITM), distributed denial-of-service (DDoS), injection, and broken access control attacks are all possible
How are APIs Abused?
The Application Programming Interface is secure by default. Difficulties arise as a result of the enormous volume of APIs deployed. Additionally, a lack of API development expertise and a failure to take into account web and cloud API security requirements may result in API vulnerabilities.
Here is a list of the top 10 API risks
Broken Object Level Authorisation
Broken Authentication
Broken Object Property Level Authorisation
Unrestricted Resource Consumption
Broken Function Level Authorisation
Unrestricted Access to Sensitive Business Flows
Server-Side Request Forgery
Security Misconfiguration
Improper Inventory Management
Unsafe Consumption of APIs
Track and Manage Web Application Security Risks and Progress with Industry Experts
Contact Us NowWhat we have done
Explore some of our projects showcasing our expertise in creating robust and scalable solutions.
Tailored Technologies to Conquer Your Development Challenges
Harness the power of our advanced technologies to elevate user interaction and drive engagement.
The Advantages of Working with Dotsquares for Development
We craft solutions that transform your business. Here's what sets us apart:
Competitive Rates
Our rates are highly competitive, ensuring that you receive excellent value for your money. With us, you can be confident that you are getting the best possible rates without compromising on quality.
Quality
We take pride in delivering exceptional results. Our CMMI level 3 appraisal and membership in the Agile Alliance demonstrate our commitment to strong processes and quality control. This ensures you get a polished, high-quality product every single time.
In-House Expertise
Our 1,000+ designers, developers, and project managers are all directly employed by us and work in our own offices across the US, UK, India, and globally. This ensures seamless collaboration and control over your project.
Security & Confidentiality
Unlike many offshore companies, security is our top priority. Your data and intellectual property remain completely confidential, and all source code rights belong to you, always.
On-Time Delivery
We use cutting-edge project management tools and agile development practices to keep your project on track. This means you'll get high-quality products delivered exactly when you expect them.

Flexible Engagement Models
We understand that your needs can change. That's why we offer flexible engagement options. Choose the model that works best for you now, and switch seamlessly if your needs evolve. We're committed to building a long-term, reliable partnership with you.
Get Our Assistance for Your Business Needs
At Dotsquares, we provide flexible options for accessing our developers' time, allowing you to choose the duration and frequency of their availability based on your specific requirements.

When you buy bucket hours, you purchase a set number of hours upfront.
- Your purchased bucket hours remain valid for 6 months, during this time frame, you can utilize our services until your hours are exhausted or until the 6-month period expires.
- For example, if you invest in 40 bucket hours and use 10 hours within the first month, you will have a remaining 30 hours to utilize over the next 5 months.
- In this case, the developer will work for other projects simultaneously as you have opted for bucket hours and not dedicated hiring.
It's a convenient and efficient way to manage your developer needs on your schedule.
Explore more
In dedicated hiring, the number of hours are not fixed like the bucket hours but instead, you are reserving the developer exclusively for your project.
- The developer will work only on your project for a set amount of time.
- You can choose to hire the developer for a week or a month, depending on what your project needs.
- This means our developer will focus exclusively on meeting the needs of your project, without any distractions from other commitments.
Whether you need help for a short time or a longer period, our dedicated hiring option ensures your project gets the attention it deserves.
Explore moreOur Agile Development Process
Companies employ developers from us because we have a proven track record of delivering high-quality projects on time.
Planning & Consultation
Our journey begins with understanding your vision. Based on your vision, we collaboratively create a project roadmap with clear milestones. We’ll consult about your ideas, target audience, and desired outcomes.
Initiate discussions to understand your objectives, target audience, and desired outcomes.
Collaboratively create a detailed project plan with clear milestones and deadlines.
Outline the key features, functionalities, and requirements.
Allocate team roles, tools, and budgets to ensure effective project management.
Design
Our skilled designers translate your vision into a user-friendly and visually appealing solution. They focus on creating a positive user experience that keeps users engaged and coming back for more.
Develop wireframes to outline the structure and layout.
Craft the user interface and user experience, focusing on aesthetics and functionality.
Create interactive prototypes for user feedback and refinement.
Present the design for your review and approval, making necessary adjustments based on feedback.
Development
Our expert developers take your design and turn it into reality. We keep you informed throughout the process with regular progress reports and milestone deliverables. This ensures you have complete transparency and control over the development phase.
Code the client-side interface, ensuring responsiveness and compatibility.
Build the server-side logic, integration, and functionalities.
Provide progress reports and milestone deliverables to keep you informed.
Conduct initial testing and debugging to ensure the development functions as intended.
Testing
Before launch, our dedicated QA specialists meticulously test every aspect of your product. They identify and fix any potential issues to guarantee a smooth and flawless user experience.
Test all features and functionalities to ensure they work correctly.
Evaluate the user interface and user experience for ease of use and navigation.
Assess the speed, load time, and responsiveness under various conditions.
Conduct thorough security checks to identify and fix vulnerabilities.
Deployment
Once everything is finalised, our team strategically chooses the most suitable deployment methods and services. Now, your project is live for everyone to see and interact with!
Recommend and set up the most suitable services based on your needs.
Perform final checks and configurations before going live.
Develop a launch plan, including marketing and promotional strategies.
Deploy the product, ensuring everything is functional and optimised for performance.
Maintenance
Our commitment doesn't end at launch. We provide ongoing support to ensure your product stays up-to-date, secure, and bug-free.
Implement software and security updates to keep the website current.
Continuously monitor performance and security to prevent issues.
Address any technical issues or bugs that arise post-launch.
Optimise speed and functionality based on user feedback and analytics.
Still not sure what you are looking for?
Connect with our experts!
Built Relationships with 12,500+ Happy Clients!
Companies employ software developers from us because we have a proven track record of delivering high-quality projects on time.

5+ Years of Average Experience

Integrity & Transparency

FREE No Obligation Quote

ISO 27001 Information Security

Outcome-Focused Approach

Transparency is Guaranteed

Focus on Security

4.8/5 Rating on Clutch

Hire a Team of Your Choice

Costs Lower Than Your Local Guy

We're here to answer all your questions.
Insecure APIs can lead to data breaches, unauthorized access to sensitive information, and service disruptions, potentially causing financial loss and reputational damage.


















































































